- Why [24]7.ai
- Products
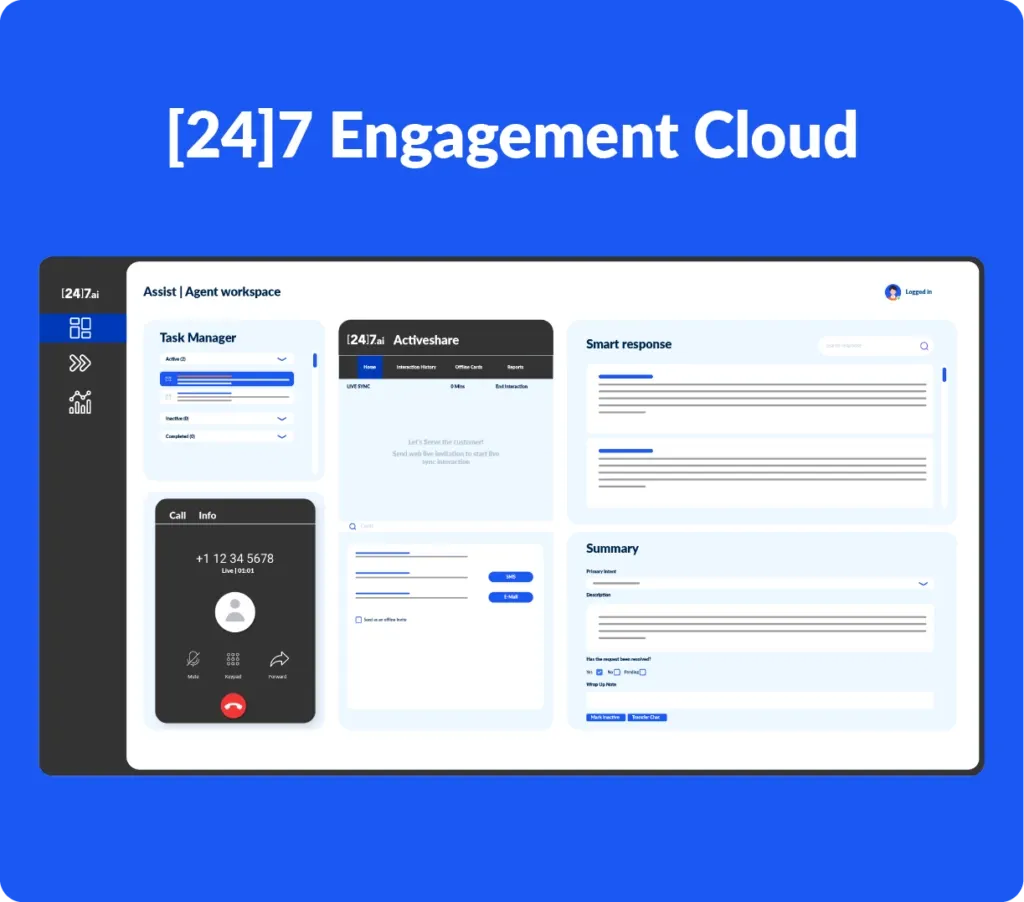 [24]7 Engagement Cloud, an AI-powered omnichannel CX platform, equips you to excel at every stage of the customer journey, from the very first interaction to building enduring relationships. A complete package that helps you acquire new customers, nurture existing ones, and drive long-term retention – all on a single, unified platform.Discover how our platform empowers customers, agents and contact center leaders to deliver exceptional CX:
[24]7 Engagement Cloud, an AI-powered omnichannel CX platform, equips you to excel at every stage of the customer journey, from the very first interaction to building enduring relationships. A complete package that helps you acquire new customers, nurture existing ones, and drive long-term retention – all on a single, unified platform.Discover how our platform empowers customers, agents and contact center leaders to deliver exceptional CX: - Services
AI-Driven CX That Delivers
Transform your CX strategy with AI-driven intelligence. Combine passionate CX brand ambassadors, predictive analytics, and intelligent automation to cultivate loyalty, craft unforgettable customer experiences, and deliver measurable business impact at scale.
- Solutions
End-To-End CX Management
Explore by Use Case
US Retailer Transforms CX with [24]7.ai Managed Customer Engagement
Gold Awards at US Customer Experience Awards, 2024
- Company
Explore [24]7.ai
Explore Locations
- Insights
- Careers
Work @ [24]7.ai
Work Locations
- Product Login and Support
- Contact Us
Security
[24]7.ai Security Standards and Risk Management Framework
[24]7.ai Security Standards

In additional to the frameworks listed in the Compliance, Privacy, and Risk Management sections, [24]7.ai internally evaluates security, privacy, risk, and security status against the U.S. Commerce Department’s National Institute of Standards and Technology (NIST) SP 800-53 R4/R5, Security and Privacy Controls for Information Systems and Organizations, and the NIST Cybersecurity Framework (CSF).
NIST 800-53 uses a systematic approach to make a comprehensive set of safeguarding measures available to a broad base of public and private sector organizations. The measures apply to all types of computing platforms, including cyber-physical systems, mobile and cloud systems, general-purpose computing systems, industrial/process control systems and IoT (Internet of Things) devices.
The NIST CSF was developed with a focus on industries vital to national and economic security, including energy, banking, communications and the defense industrial base. It has since proven flexible enough to be adopted voluntarily by large and small companies and organizations across all industry sectors, as well as by federal, state and local governments.
Risk Management Framework

The American Institute of Certified Public Accountants (AICPA) revised its Trust Services Principles and Criteria, known as the TSP in 2018 making it mandatory for SOC 2 reports dated after December 15, 2018 to more accurately align with the Committee of Sponsoring Organizations’ (COSO) 2013 Framework.
The COSO 2013 Framework, like the 2017 Trust Services Criteria, treats risk management as an ongoing process that starts with upper management and requires buy-in from all stakeholders in order to identify the relevant risks and remediation options.
At least once a year, management and relevant oversight groups (i.e. Board of Directors) should facilitate a discussion of the enterprise’s obligations, threats to completion and ways of mitigating those threats. We strongly recommend quarterly follow-up meetings to identify and discuss any changes. Mitigation is not a static endeavor: threats evolve, and so should your risk-management plan.
The process also must be formalized and documented in order to validate and support operating effectiveness throughout the period in scope.
Compliance Overview

In addition to our 3rd party tested SOC 2 Type 2, [24]7 is compliant with Health Insurance Portability and Accountability Act (HIPAA). We ensure our compliance with all HIPAA Rules (Privacy, Security, and Breach Notification) and adhere to the regulated Administrative, Physical, and Technical Safeguards. [24]7 is dedicated to securing any Protected Health Information (PHI) or Electronic Protected Health Information (ePHI) at all times. For more information on HIPAA rules and regulations, visit the U.S. U.S. Department of Health and Human Services website.

ISO/IEC 27001:2022 is a security management standard that specifies security management best practices and comprehensive security controls following the ISO/IEC best practice guidance. The basis of this certification is the development and implementation of a rigorous security program, which includes the development and implementation of an Information Security Management System (ISMS) which defines how [24]7.ai perpetually manages security in a holistic, comprehensive manner. This widely-recognized international security standard specifies that [24]7.ai do the following:
- We systematically evaluate our information security risks, taking into account the impact of threats and vulnerabilities.
- We design and implement a comprehensive suite of information security controls and other forms of risk management to address customer and architecture security risks.
- We have an overarching management process to ensure that the information security controls meet our needs on an ongoing basis.
The certification is performed by independent third-party auditors. Our compliance with this internationally-recognized standard and code of practice is evidence of our commitment to information security at every level of our organization, and that the [24]7.ai security program is in accordance with industry leading best practices.

The Payment Card Industry Data Security Standard (PCI DSS) is a proprietary information security standard administered by the PCI Security Standards Council, which was founded by American Express, Discover Financial Services, JCB International, MasterCard Worldwide and Visa Inc.
PCI DSS applies to all entities that store, process, or transmit cardholder data (CHD) or sensitive authentication data (SAD), including merchants, processors, acquirers, issuers, and service providers. The PCI DSS is mandated by the card brands and administered by the Payment Card Industry Security Standards Council.
In addition to our own compliance, [24]7.ai is committed to offering services and resources to our customers to help them comply with PCI DSS requirements that may apply to their activities.
Increasingly, businesses outsource basic functions to service organizations. In response, the American Institute of Certified Public Accountants (AICPA) developed the Service Organization Controls (SOC) framework, a standard for controls that safeguard the confidentiality and privacy of information stored and processed by service organizations. This aligns with the International Standard on Assurance Engagements (ISAE), the reporting standard for international service organizations.
[24]7.ai a SOC 2 Type 2 attestation, which ensures we have met the criteria for managing customer data based on five AICPA Trust Service Principles and Criteria: Security, Availability, Processing, Integrity, and Privacy.
Privacy Framework

The European Union’s General Data Protection Regulation (GDPR) protects European Union data subjects' fundamental right to privacy and the protection of personal data. It introduces robust requirements that will raise and harmonize standards for data protection, security, and compliance.
The compliance is verified by independent third-party auditors. Our compliance with this internationally-recognized standard and code of practice is evidence of our commitment to information security at every level of our organization, and that the [24]7.ai security program is in accordance with industry leading best practices.

The California Consumer Privacy Act (CCPA) was enacted into law on June 28, 2018. The CCPA seeks to ensure California consumers have a certain level of privacy rights.
In addition to our own compliance, [24]7.ai is committed to offering services and resources to our customers to help them comply with CCPA requirements that may apply to their activities.

The APEC Framework, published by the Asia-Pacific Economic Cooperation, is a framework to protect privacy within and beyond economies and to enable regional transfers of personal information benefits consumers, businesses, and governments. This framework is used as a basis for the APEC Cross-Border Privacy Rules (CBPR) System.
In addition to our own compliance, [24]7.ai is committed to offering services and resources to our customers to help them comply with APEC CBPR requirements that may apply to their activities and are listed in the global forum listing for all organisation under APEC CBPR.
The compliance is verified by independent third-party auditors. Our compliance with this internationally-recognized standard and code of practice is evidence of our commitment to information security at every level of our organization, and that the [24]7.ai security program is in accordance with industry leading best practices.

The Data Privacy Framework aims to enable the compliant transfer of personal data from data controllers in the EU to data controllers (or processors) in the US. [24]7.ai offers customers a Data Processing Addendum, including Model Clauses (Data Processing Addendum) by the EU data protection authorities, known as the Article 29 Working Party. This Data Processing Addendum enables our customers, when using [24]7.ai to transfer personal data outside the European Economic Area (EEA), to any country, including to the US. For this reason, the Data Privacy Framework does not affect the way customers use, or work, with [24]7.ai. Customers can transfer data from EU regions to the US regions with the knowledge that [24]7.ai is compliant with EU data protection requirements.
National Privacy Commission

The National Privacy Commission (NPC) is the Philippines' data privacy authority enforcing the Data Privacy Act. It mandates that Personal Information Controllers (PICs) and Processors (PIPs) register via the NPCRS portal, appoint a Data Protection Officer (DPO), and display an NPC Seal of Registration. [24]7.ai is registered and hence displaying the seal as mandated.
Frequently Asked Questions
When providing services to a customer, [24]7.ai may transfer personal data outside of EEA, Switzerland and UK in its capacity as processor. The General Data Protection Regulation (GDPR) has been incorporated into UK’s domestic legislation, and therefore the data transfer mechanism permitted under the GDPR for transfers of personal data.
When providing services to a customer, [24]7.ai may transfer personal data outside of EEA, Switzerland and UK in its capacity as processor. The General Data Protection Regulation (GDPR) has been incorporated into UK’s domestic legislation, and therefore the data transfer mechanism permitted under the GDPR for transfers of personal data.
When providing services to a customer, [24]7.ai may transfer personal data outside of EEA, Switzerland and UK in its capacity as processor. The General Data Protection Regulation (GDPR) has been incorporated into UK’s domestic legislation, and therefore the data transfer mechanism permitted under the GDPR for transfers of personal data.
When providing services to a customer, [24]7.ai may transfer personal data outside of EEA, Switzerland and UK in its capacity as processor. The General Data Protection Regulation (GDPR) has been incorporated into UK’s domestic legislation, and therefore the data transfer mechanism permitted under the GDPR for transfers of personal data.
When providing services to a customer, [24]7.ai may transfer personal data outside of EEA, Switzerland and UK in its capacity as processor. The General Data Protection Regulation (GDPR) has been incorporated into UK’s domestic legislation, and therefore the data transfer mechanism permitted under the GDPR for transfers of personal data.